Risk Management Enterprise Fundamentals Explained
Table of ContentsThe 6-Second Trick For Risk Management EnterpriseRisk Management Enterprise for BeginnersExamine This Report on Risk Management EnterpriseThe smart Trick of Risk Management Enterprise That Nobody is DiscussingAll About Risk Management EnterpriseThe Basic Principles Of Risk Management Enterprise The 6-Minute Rule for Risk Management Enterprise
Below are some of its vital attributes that centers need to understand. So, have a look. Real-Time Threat Evaluations and Mitigation in this software enable companies to constantly keep track of and review dangers as they develop. This feature leverages real-time data and computerized analysis to identify prospective dangers without delay. Once threats are identified, the software program helps with prompt mitigation actions.
KRIs address the problem of inconsistent or uncertain threat evaluation. They address the obstacle of recurring threat management by offering tools to monitor risks constantly. KRIs enhance security risk oversight, making certain that potential threats are identified and taken care of efficiently. The job of danger monitoring must not be a challenge. Therefore, organizations have to count on an excellent and innovative danger management software program.
The 8-Minute Rule for Risk Management Enterprise
IT run the risk of management is a part of enterprise threat administration (ERM), designed to bring IT take the chance of in accordance with an organization's risk appetite. IT take the chance of monitoring (ITRM) includes the policies, procedures and innovation needed to reduce dangers and vulnerabilities, while preserving conformity with suitable governing demands. In addition, ITRM seeks to restrict the consequences of harmful occasions, such as safety violations.
Veronica Rose, ISACA board supervisor and an info systems auditor at Metropol Corp. The ISACA Threat IT structure straightens well with the COBIT 2019 framework, Rose claimed.
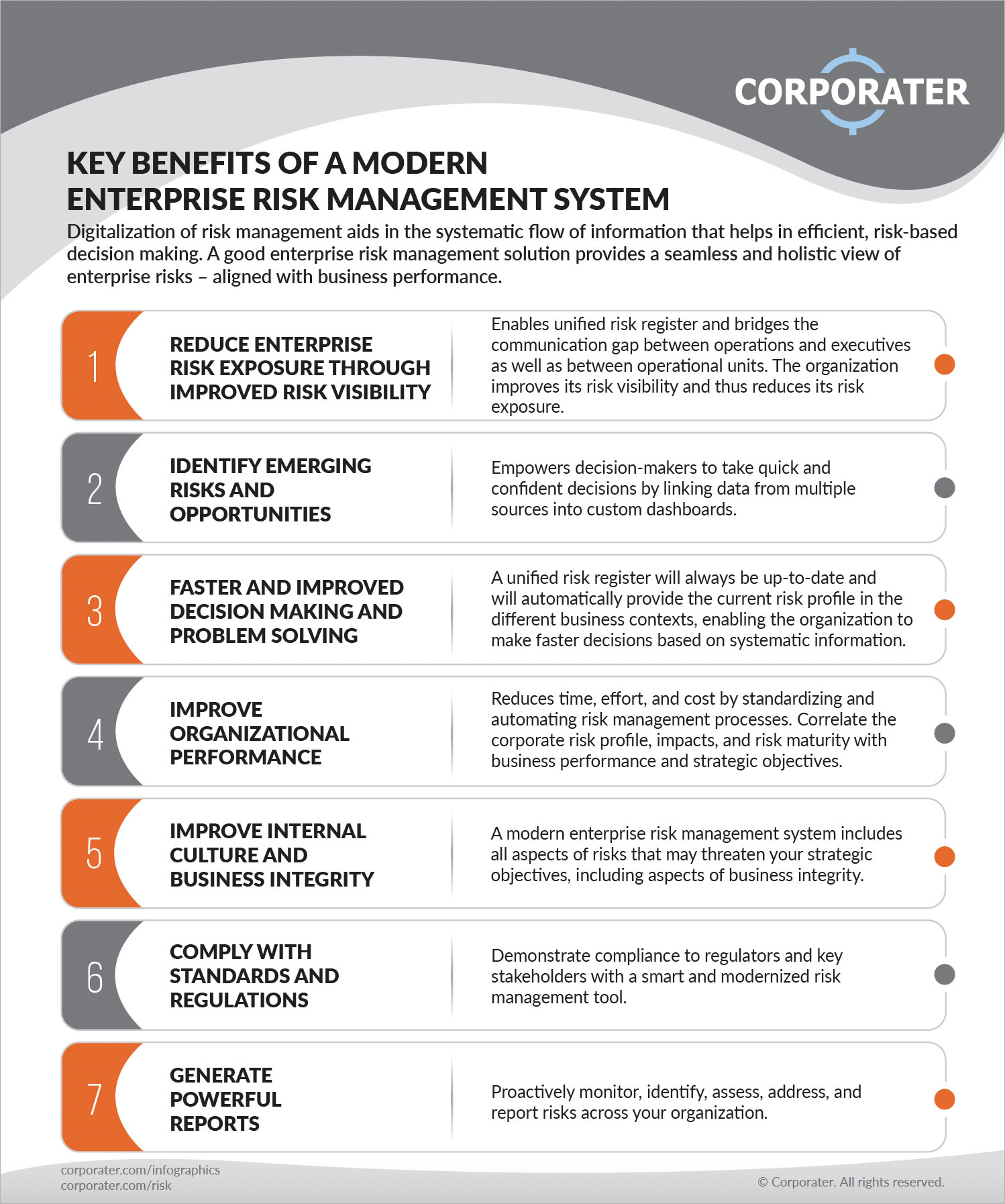
Business Threat Administration Software Application Growth: Benefits & Characteristics, Cost. With technical developments, threats are continually increasing. That being claimed, companies are more probable to face difficulties that affect their financial resources, operations, and online reputation. From swiftly varying markets to regulative modifications and cyber threats, services browse through a frequently altering sea of dangers.
The Single Strategy To Use For Risk Management Enterprise
In this blog, we will certainly study the globe of ERM software, discovering what it is, its advantages, functions, and so on to ensure that you can construct one for your business. Enterprise Threat Management (ERM) software is the application program for planning, guiding, arranging, and managing company tasks and improving threat monitoring processes.
With ERM, companies can make informative choices to improve the overall resilience of the organization. Dedicated ERM systems are crucial for businesses that routinely deal with vast quantities of delicate information and multiple stakeholders to approve tactical choices.
It can be stayed clear of by utilizing the ERM software application system. This system automates policy compliance monitoring to maintain the company safe and compliant.
The Basic Principles Of Risk Management Enterprise
You can likewise attach existing software systems to the ERM via APIs or by including information manually. Businesses can use ERM to review dangers based upon their potential influence for better risk monitoring and mitigation.: Adding this attribute allows individuals to get real-time notices on their devices concerning any type of risk that could take place and its effect.
Rather, the software program permits them to establish thresholds for various procedures and send out push notices in case of possible threats.: By integrating data visualization and reporting address in the customized ERM software program, organizations can gain clear insights concerning danger patterns and performance.: It is required for companies to stick to sector compliance and regulatory standards.
These systems allow firms to implement best-practice risk management processes that straighten with sector standards, try this website supplying an effective, technology-driven method to determining, assessing, and mitigating risks. This blog checks out the benefits of computerized risk administration devices, the locations of threat management they can automate, and the worth they offer an organization.
Get This Report on Risk Management Enterprise
Groups can set up forms with the appropriate fields and quickly develop different forms for different threat types. These risk analysis types can be distributed for completion by means of automated process that send notices to the pertinent team to complete the types online. If kinds are not completed by the due date, after that chaser emails are automatically sent out by the system.
The control tracking and control testing process can likewise be automated. Firms can utilize computerized workflows to send out routine control test notifications and staff can go into the results through on the internet kinds. Controls can additionally be monitored by the software by establishing rules to send out informs based upon control information kept in other systems and spread sheets that is pulled right into the system using API assimilations.
Risk management automation software can also support with risk coverage for all levels of the venture. Leaders can watch records on risk direct exposure and control effectiveness through a selection of reporting outcomes consisting of fixed records, Power BI interactive reports, bowtie evaluation, and Monte Carlo simulations. The capability to draw actual time records at the touch of a button eliminates arduous information control why not find out more tasks leaving risk groups with even more time to analyze the data and advise the service on the finest course of action.
The need for efficient has actually never been a lot more important. Risk Management Enterprise. Organizations operating in competitive, fast-changing markets can not afford delays or inefficiencies in addressing prospective threats. Typical risk management making use of hands-on spreadsheet-based processes, while acquainted, commonly cause fragmented data, taxing coverage, and a boosted possibility of human mistake. Automating the threat administration procedure with software program addresses these imperfections.
An Unbiased View of Risk Management Enterprise
This ensures danger registers are constantly present and straightened with business purposes. Conformity is one more important motorist for automating threat monitoring. Standards like ISO 31000, CPS 230 and COSO all offer support around danger management best practices and control frameworks, and automated danger management devices are structured to straighten with these demands helping companies to satisfy most frequently used risk management requirements.
Try to find threat software systems with a consents hierarchy to quickly establish up workflows for risk rise. This performance allows you to tailor the view for each and every customer, so they only see the information appropriate to them. Make sure the ERM software program uses user monitoring so you can see who entered what information and when.
Look for out tools that use project danger monitoring abilities to handle your tasks and portfolios and the connected dangers. The benefits of taking on risk administration automation software program extend far beyond performance.
The Best Guide To Risk Management Enterprise
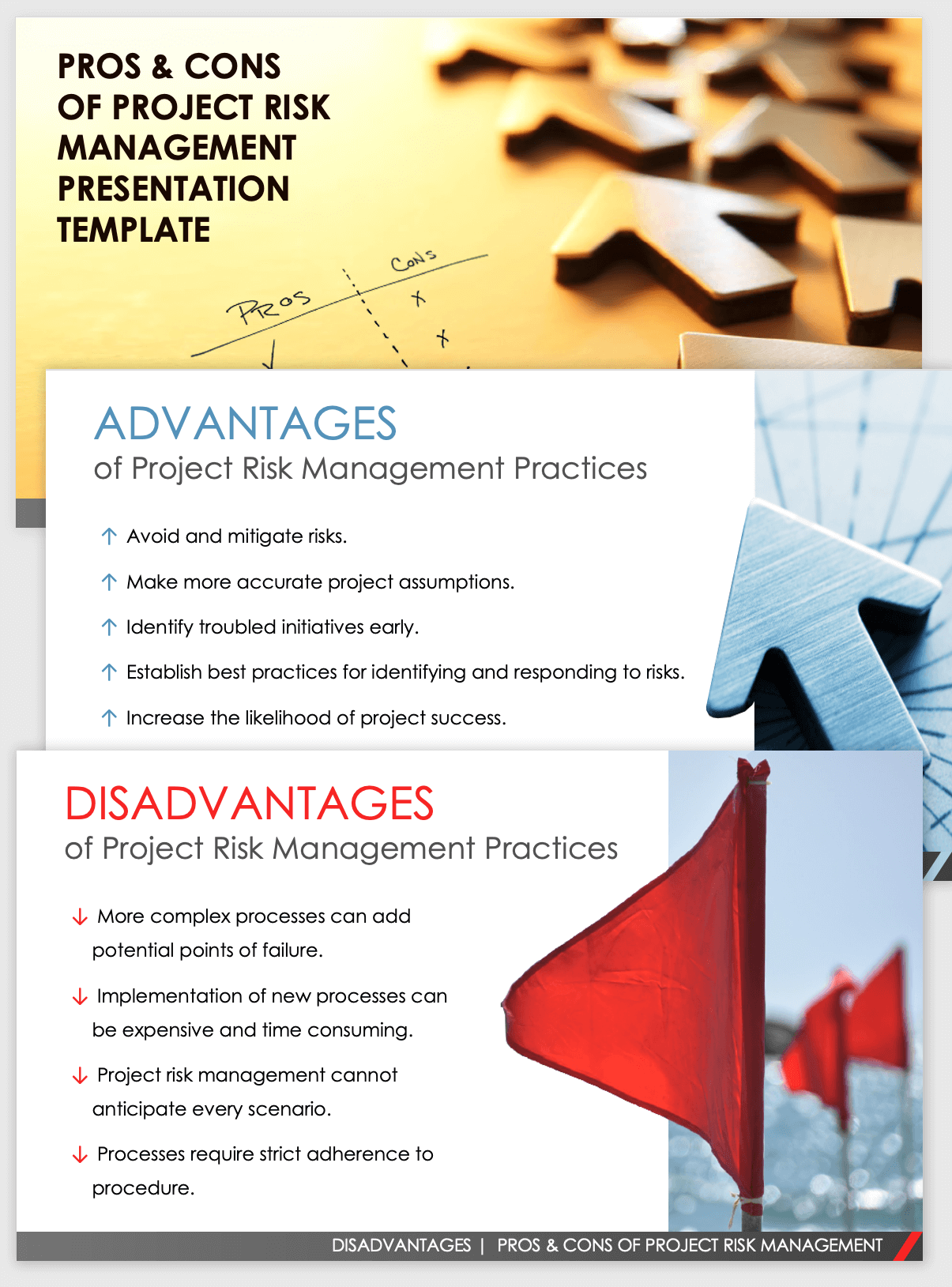
While the case for automation is engaging, applying a danger management system is not without its challenges. To get over the difficulties of risk monitoring automation, organizations should invest in data cleansing and governance to ensure a solid structure for executing an automated platform.
Automation in risk management equips companies to change their strategy to risk and develop a stronger foundation for the future (Risk Management Enterprise). The inquiry is no longer whether to automate threat management, it's how quickly you can start. To see the Riskonnect at work,
The answer commonly exists in how well threats are prepared for and handled. Project administration software works as the navigator in the tumultuous waters of task implementation, offering tools that identify and analyze dangers and create methods to alleviate them successfully. From real-time information analytics to detailed threat surveillance dashboards, these tools supply a 360-degree sight of the task landscape, enabling task supervisors to make enlightened decisions that keep their tasks on course and within spending plan.